How to Build an AI Agent That Pays with USDC
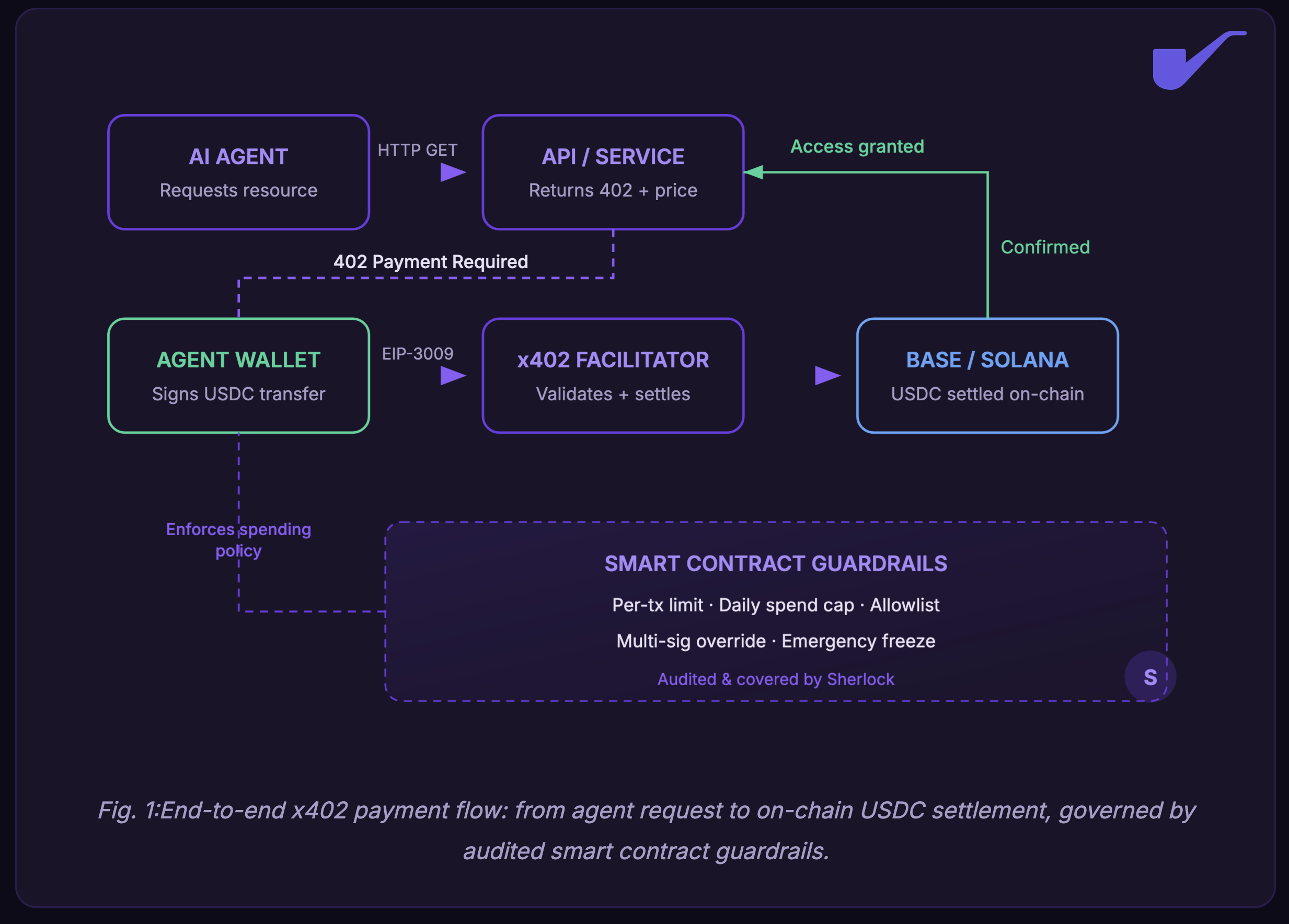
AI agents are already making USDC payments on-chain. This guide covers wallet setup, x402 integration, spending controls, and the security model needed to protect agent funds in production.

Sherlock Engineering · March 2026
Autonomous agents are already transacting at scale. This is the practical architecture for giving your agent a USDC-powered wallet, and the security model required to protect it.
Something shifted in the last twelve months. AI agents went from demo curiosities to economic participants. Circle reports that in the nine months leading into March 2026, agents completed over 140 million payments totaling $43 million, with 98.6% settled in USDC. More than 400,000 agents now hold purchasing power on-chain. The question has moved past "will agents transact autonomously?" to "how do you build that capability correctly from day one?"
This guide walks through the full stack: wallet provisioning, the payment protocol your agent will speak, the smart contract layer that enforces spending rules, and the security architecture required to protect real funds in production.
Why USDC for Agent Payments
Traditional payment rails were not designed for machine-to-machine commerce. Credit card networks require identity verification, session management, and human-readable UIs, none of which apply when two programs are negotiating a data purchase in 200 milliseconds. USDC removes those friction points. It is programmable, settles in seconds on chains like Base and Solana, and maintains a stable dollar peg, so your agent's treasury holds its value regardless of market conditions.
The catalyst for agent-native payments arrived when Coinbase open-sourced the x402 protocol, a standard that revives the long-dormant HTTP 402 "Payment Required" status code and pairs it with on-chain USDC settlement. In practice, an agent hits an API, receives a 402 response containing a price and payment address, signs a USDC transfer, and gets access, all without accounts, API keys, or manual intervention. Stripe has already integrated x402 into its platform for agent-to-service payments on Base, and CoinGecko activated it for API access at $0.01 USDC per request.
The Architecture, Step by Step
Step 1: Generate a dedicated agent wallet using MPC. Your agent needs its own key pair and on-chain address, fully isolated from any human-controlled treasury. The fastest path is the Coinbase CDP SDK (npm install @coinbase/cdp-sdk), which creates MPC-backed wallets programmatically. MPC splits the key material across multiple parties, so no single compromised server can sign a transaction. Configure the wallet so your agent holds signing authority for day-to-day operations while a human admin retains freeze and recovery access through a separate key shard. Fund the wallet with USDC on Base (lowest fees, native USDC support) or Solana (higher throughput). You can get testnet USDC from the CDP quickstart to validate the setup before going live.
Step 2: Install and configure the x402 payment client. The x402 SDK is modular. For a fetch-based agent, run npm install @x402/fetch @x402/evm. For axios-based agents, swap in @x402/axios. If your agent transacts on Solana, add @x402/svm. Full package list and docs are on the x402 GitHub repo. The SDK intercepts HTTP 402 responses, parses the payment requirements (amount, recipient address, supported chains), and constructs a USDC transfer using the EIP-3009 standard. EIP-3009 enables gasless transfer authorizations: your agent signs a message off-chain, and the x402 facilitator submits the actual on-chain transaction, so the agent never needs to hold ETH for gas. Total round-trip on Base is typically under two seconds. The buyer quickstart guide walks through the full integration in under 30 minutes.
Step 3: Deploy a guardian smart contract with spending rules. This is the layer most teams underestimate. Without constraints, an agent with a funded wallet is an open checkbook. Write and deploy a guardian contract that sits between the agent wallet and the x402 facilitator, enforcing per-transaction ceilings, rolling daily spend caps, and a strict allowlist of approved recipient addresses. Use OpenZeppelin's Solidity contract libraries as a foundation for access control and pausable patterns rather than writing them from scratch. Include a multi-sig override function that lets authorized humans freeze all outflows in a single call. Keep the guardian contract's logic minimal: the fewer code paths, the smaller the attack surface. This contract should be formally audited before it touches real funds.
Step 4: Build the observability and logging pipeline. Every transaction your agent makes should be logged with full context: what resource it purchased, the price in USDC, the counterparty address, the on-chain tx hash, a timestamp, and the business reason (the agent's internal decision that triggered the purchase). Pipe these logs into a structured data store where you can query spend by service, by time window, and by decision category. For on-chain monitoring, tools like Tenderly or Forta can watch your guardian contract for anomalous calls and trigger alerts via webhook. This data is how you debug cost overruns, catch duplicate payments, and build the case for expanding the agent's budget as it proves ROI.
Step 5: Set up automated treasury monitoring and replenishment. Your agent's USDC balance will deplete over time, and the rate may vary unpredictably. Configure automated alerts that fire when the balance drops below a threshold (20% of the initial fund is a reasonable starting point) and build a replenishment flow. This can be a manual approval step routed to a treasury multisig, or an automated top-up from a parent wallet that has its own independent spending cap. Track the agent's burn rate weekly and compare it against the value the agent generates so you can confirm the economics hold before scaling up.
Step 6: Write the incident response and key rotation runbooks. Before your agent processes its first real payment, document two runbooks. The incident response playbook should cover: who gets paged when monitoring flags unexpected behavior, how to freeze the wallet within 60 seconds via the guardian contract's pause function, how to investigate the root cause, and how to resume operations. The key rotation playbook should cover the full cycle: generating the new key shard through your MPC provider, updating all dependent services, verifying the new key end to end in staging, and revoking the old one. MPC providers simplify rotation compared to raw key management, but you still need a documented, tested process. Run both runbooks in staging before going live.
Security and Maintenance
A bug in your guardian contract could drain your agent's treasury in seconds. The standard lifecycle for securing a smart contract applies here: AI-assisted code review during development, a formal audit or contest to stress-test the contract adversarially, and post-launch bug bounties. As your agent's responsibilities grow, the spending rules from launch will need to evolve. If your guardian uses an upgradeable proxy, plan changes through a governance process. If immutable, plan for contract migration well in advance of hitting limits. As industry leaders from Visa to Coinbase have acknowledged, any contract that controls agent spending needs the same rigor as a DeFi protocol's core logic.
Where Agent Payments Are Heading
Within the next 12 to 18 months, the number of autonomous agents making payments on-chain will likely exceed the number of humans doing the same. The x402 Foundation, backed by Cloudflare, Google, Visa, AWS, Circle, Anthropic, and Coinbase, is standardizing the protocol layer. Cross-chain agent payments (transacting across Base, Solana, and Ethereum L2s without manual bridging) are in active development. Fiat on-ramps that let agents top up their own wallets via ACH are in beta. Teams building token ecosystems in 2026 are already embedding these patterns into their architectures.
This guide will be updated as the technology develops. We plan to cover multi-chain agent wallets, fiat-to-USDC on-ramps for agents, and evolving regulatory frameworks in future editions.
If you are building AI agents that transact on-chain and want to talk through your security architecture, get in touch with our team.


.png)